As Apple's popularity grows, so does the desire among fraudsters to make money from the people who own the company's devices.
Research and publish the best content.
Get Started for FREE
Sign up with Facebook Sign up with X
I don't have a Facebook or a X account
Already have an account: Login
Related articles to 21st Century Learning and Teaching as also tools...
Curated by
Gust MEES
 Your new post is loading... Your new post is loading...
 Your new post is loading... Your new post is loading...
|










===> As Apple's popularity grows, so does the desire among fraudsters to make money from the people who own the company's devices. <===
On some days the number of web antivirus detections for fake apple.com phishing sites exceeded the daily average by several times. There were a number of peaks, the most significant of which occurred on December 6, 2012 (939,549 detections) and May 1, 2013 (856,025 detections).
This periodic surge in cybercriminal activity and the resulting increase in web antivirus detections can be put down to important events in the life of Apple. For example, December's peak occurred immediately after the iTunes Store opened in Russia, Turkey, India, South Africa and 52 other countries around the world.
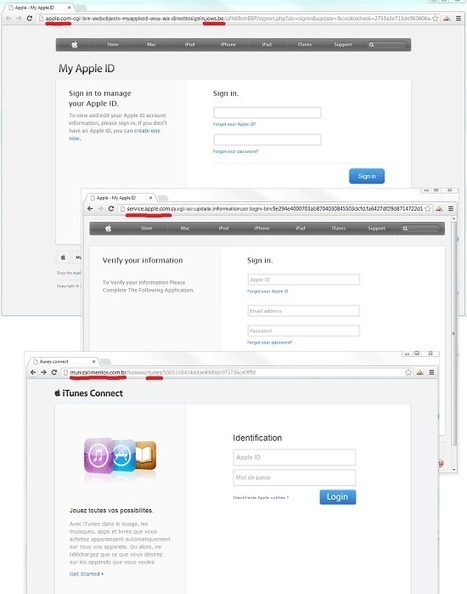
How do users end up on fake sites? One of the most popular methods is to use spam to spread links to phishing sites. For example, cybercriminals send out emails on behalf of Apple in which they ask the recipient to confirm their account by following a link in the message.
The link leads to a fake website where users are asked to enter their Apple ID and password - this data is then stolen by the cybercriminals and used for their own ends.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
===> As Apple's popularity grows, so does the desire among fraudsters to make money from the people who own the company's devices. <===
On some days the number of web antivirus detections for fake apple.com phishing sites exceeded the daily average by several times. There were a number of peaks, the most significant of which occurred on December 6, 2012 (939,549 detections) and May 1, 2013 (856,025 detections).
This periodic surge in cybercriminal activity and the resulting increase in web antivirus detections can be put down to important events in the life of Apple. For example, December's peak occurred immediately after the iTunes Store opened in Russia, Turkey, India, South Africa and 52 other countries around the world.
How do users end up on fake sites? One of the most popular methods is to use spam to spread links to phishing sites. For example, cybercriminals send out emails on behalf of Apple in which they ask the recipient to confirm their account by following a link in the message.
The link leads to a fake website where users are asked to enter their Apple ID and password - this data is then stolen by the cybercriminals and used for their own ends.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security