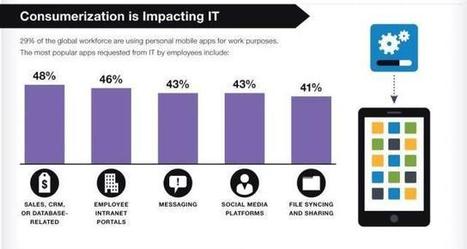
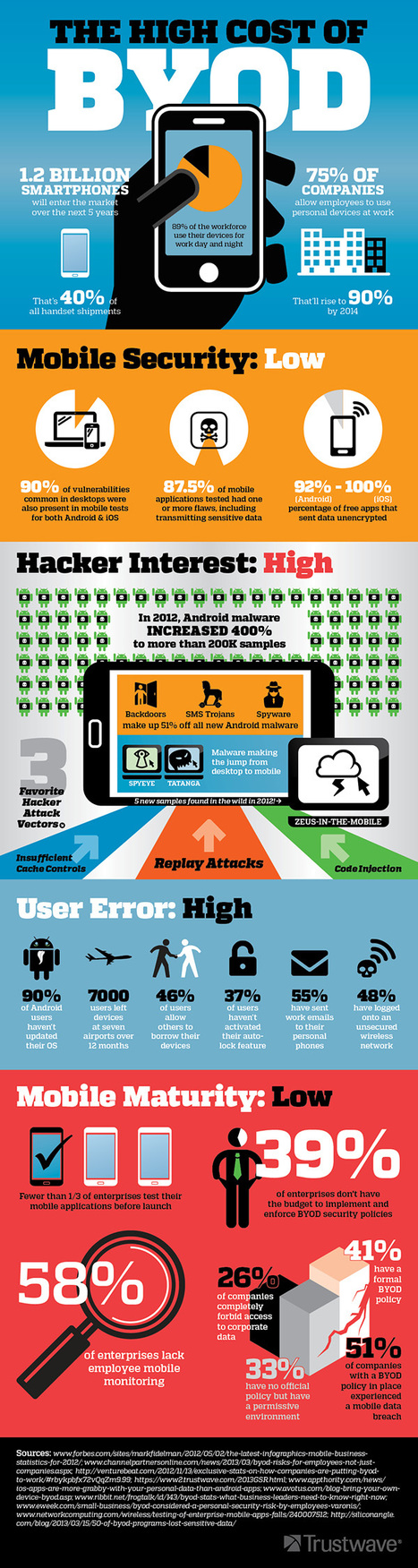
De plus en plus d’employés emmènent leurs appareils au travail et se connectent sur le réseau de l’entreprise.
Get Started for FREE
Sign up with Facebook Sign up with X
I don't have a Facebook or a X account
 Your new post is loading... Your new post is loading...
 Your new post is loading... Your new post is loading...

Gust MEES's curator insight,
May 14, 2013 5:11 PM
Read the full article to understand really...
Learn more:
- http://gustmees.wordpress.com/2013/05/13/visual-cyber-security-see-attacks-on-real-time/

asma jmari 's comment,
May 20, 2013 6:34 AM
believe it or not they do and hacking is more like a hobby some do it for fun and some just dedicate themselves to it and make it a job

Mike Hodges Eirias's curator insight,
May 8, 2013 3:56 AM
So you don't have to be a big business to be affected by the DPA! |

Gust MEES's curator insight,
March 4, 2013 11:06 AM
===> Unfortunately, the playing surface for Internet naughtiness has changed in the past couple of years and you need to know that it's only getting worse. <===
Check also:
- http://www.scoop.it/t/apps-for-any-use-mostly-for-education-and-free

alistairm 's curator insight,
March 5, 2013 3:35 AM
Oh dear - the world of technology seems to be one step forward two steps back but these issues are important especially of we are going to be using mobile devices in education and promoting BYOD approaches. |










![Why You Should Care About Mobile Security [INFOGRAPHIC] | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/bCDzCBQu4qMgWJAbygdm2jl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)
![BYOD: Bring Your Own Risk (BYOR) [INFOGRAPHIC] | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/y5NTg9uYlSpK6x67Mbb7WDl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)


![BYOD: Mobility making it easier for insiders to take IP [Infographic] | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/7qGVluSAqAo_xdmrGdGXozl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)







Learn more:
- https://www.cases.lu/fr/byod-un-risque-et-une-opportunite-en-meme-temps.html