Bringing your own device to work may be beneficial to the worker, but what about when personal citizen data gets loaded on to such devices? British authorities are firing off the warning flares.
The ICO this week published its latest guidance note [PDF] on some of the risks that employers face when allowing personal devices into the enterprise. While BYOD is on the rise in the U.K., employers must still remember that the Data Protection Act—which stems from a 1995 European directive—still applies to these devices.



 Your new post is loading...
Your new post is loading...



![Adoption Rates of New Styles of K-12 Teaching [Infographic] - BYOD | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/7CwBx2opz0RQK34FnQvyPDl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)




![Why You Should Care About Mobile Security [INFOGRAPHIC] | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/bCDzCBQu4qMgWJAbygdm2jl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)















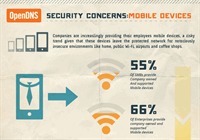





So you don't have to be a big business to be affected by the DPA!