I feel so alive.
Get Started for FREE
Sign up with Facebook Sign up with X
I don't have a Facebook or a X account

 Your new post is loading... Your new post is loading...
 Your new post is loading... Your new post is loading...
An in-depth article and infographic on how blended learning is changing education.
THE OFFICIAL ANDREASCY's insight:
Technology has changed education and has expanded student opportunities. Get the scoop! 
Andreas Christodoulou's curator insight,
August 1, 2016 6:05 AM
Analysis of more than 1,000 learning studies by the department of education show blended learning environments have the greatest impact in improving student achievement. We cover three main types of blended learning models; traditional, hybrid and flipped. We also tackle five common misconceptions about blended learning: http://tiny.cc/BlendedLearningPotential 
Stephania Savva, Ph.D's curator insight,
August 1, 2016 6:09 AM
A really useful article on Blended Learning and the prospect of differentiating teaching and learning strategies.
There's a lot of exciting developments happening in the world of technology - don't fall behind. Sign up so we can keep in touch.
THE OFFICIAL ANDREASCY's insight:
The newsletter will boil it all down for you, providing only the most relevant information and sending it straight to your inbox. We also offer insightful tips, tricks and time-saving techniques with fresh and useful resources.
Click here to sign up for it. See you on the inside! ;) 
Jane Shamcey's curator insight,
June 8, 2015 7:12 AM
The best way to keep on top of the latest tech information is to subscribe to our newsletter: http://swyy.co/EAqLdtE 
Stephania Savva, Ph.D's curator insight,
June 8, 2015 7:14 AM
Seek no further for reliable and up to date tech news from around the globe delivered right to your inbox. Also check their latest tweets: https://twitter.com/andreaschriscy
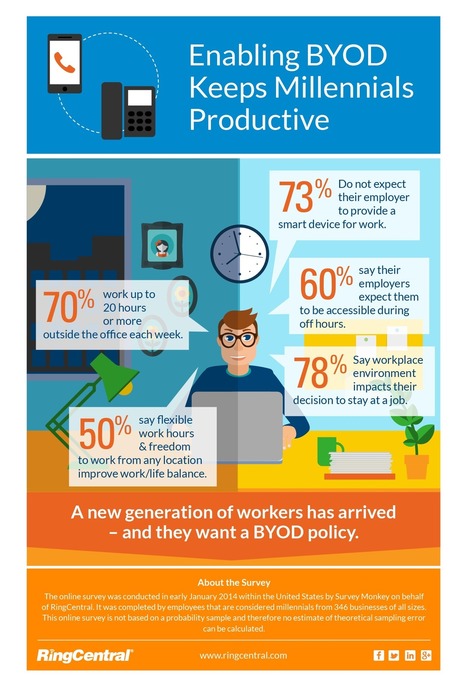
Ask anyone under 33 what they look for in a job, and chances are they’ll tell you it’s flexibility. Via Tom D'Amico (@TDOttawa) , John Purificati
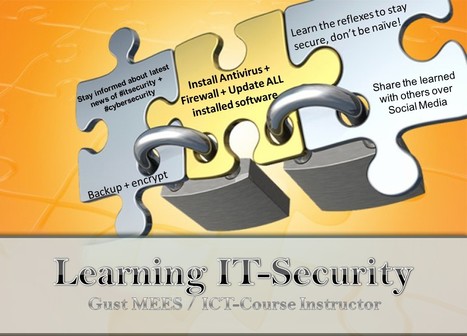
Security researchers have discovered a vulnerability that could allow attackers to take full control of most Android smartphones
The vulnerability allows hackers to modify an app without breaking its cryptographic signature, according to Jeff Forristal, chief technology officer (CTO) at mobile security firm Bluebox.
Via Gust MEES, TechinBiz 
Gust MEES's curator insight,
July 4, 2013 6:45 AM
The vulnerability allows hackers to modify an app without breaking its cryptographic signature, according to Jeff Forristal, chief technology officer (CTO) at mobile security firm Bluebox. 
Gust MEES's curator insight,
July 4, 2013 6:48 AM
The vulnerability allows hackers to modify an app without breaking its cryptographic signature, according to Jeff Forristal, chief technology officer (CTO) at mobile security firm Bluebox. 
Zhao KQiang's curator insight,
March 27, 2014 6:52 AM
there is one example of smart phone security. focus on the mobile system Android
Bring Your Own Device (BYOD) is more complex than most people know, read further to learn… . .
Keywords for this free course: . motivation, engagement, heroes, Security-Scouts, critical thinking, stay out of the box, adapt to new technologies, be aware of the malware, nobody is perfect, knowing the dangers and risks, responsibility, responsibility of School, responsibility of IT-Admin, responsibilities of BYOD users, Apple insecurity, Insecurity of Apps, Principals responsibilities, Mobile Device Management, risks of BYOD, BYOD-Policy, IT-Security Infrastructure, Teacher-Parents Meeting, Cyberwar, Cyberwarfare, Government, Internet-Safety, IT-Security knowledge basics...
The weakest link in the Security Chain is the human! If you don’t respect certain advice you will get tricked by the Cyber-Criminals!
Read more: http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/
Via Gust MEES, kallen214
Gary Harwell's curator insight,
April 3, 2013 12:47 AM
Is ti possible that we have a special room for this?
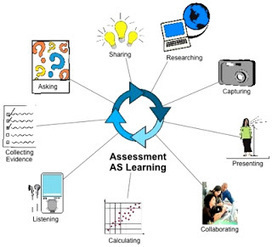
What will Personalized Learning look like in 2013? The main change that will happen in teaching and learning in 2013 will be about empowerment. Teachers and learners will be more empowered to take charge of their learning. We will see this through the evidence they share as they learn. Via Kathleen McClaskey, Barbara Bray 
Thomas Salmon's curator insight,
May 6, 2013 1:34 PM
Interesting, in other ways this could also be seen as framing learning as a constant performance of assessment. Where do you draw the line ? |
How to nurture learning for young people to take on the challenges of the digital world.
THE OFFICIAL ANDREASCY's insight:
Is it possible to make learning accessible and meaningful for digital natives? 
Stephania Savva, Ph.D's curator insight,
March 17, 2017 11:37 AM
You might want to check out this article on ways to enhance your students' learning. It is not an easy case to engage digital natives, yet it is possible.

Jemma Wilson's curator insight,
May 9, 2017 6:36 AM
Interesting take on digital pedagogy - Flip side, that in this digital world we as teachers must remain personable - but still the focus is that we have something to teach! Purpose purpose purpose!
In the Derry Township School District in Hershey, PA, students as young as the fourth grade are allowed to bring their own devices to class to support their learning, at the discretion of their teacher. Via Tom D'Amico (@TDOttawa) , Stephania Savva, Ph.D 
RESENTICE's curator insight,
October 26, 2015 6:37 AM
Comment surmonter les difficultés engendrées par l'utilisation de smartphones en classe ? 
Charmaine Hamann's curator insight,
October 31, 2015 9:34 AM
While this ceates challenges for equity of resources and IT security infrastructure for schools, it is a practice model used successfully in some European schools as well! Digital natives would be able to bring more to the table that they are already comfortable with in their home environment.
From
tech
BYOD (bring your own device) is being adopted by hundreds of schools due to its positive impact on learning. See how it's shaping education. Via Tom D'Amico (@TDOttawa)
THE OFFICIAL ANDREASCY's insight:
Tricia Paparo's curator insight,
April 26, 2015 8:30 AM
I love this article and the picture along with it. I especially enjoy how the teacher is standing behind the students to make sure that she can monitor them as they work.
The BYOD Pros and Cons in Education Infographic highlights many of the advantages and disadvantages to letting students use personal devices in the classrooms. Via Tom D'Amico (@TDOttawa)
Anne-Maree Johnson's curator insight,
April 7, 2014 5:17 PM
Pros and cons of BYOD presented as an infographic. American but still applies in an Australian setting. 
Bryan Wiedeman's curator insight,
October 11, 2014 2:27 AM
A great resource to share with faculty and families to help build support for the adoption of BYOD. I particularly like the pros and cons image at the bottom which illustrates some of the important issues related to BYOD in schools.
#sidebar-second { Via Tom D'Amico (@TDOttawa)
Bring Your Own Device (BYOD) is more complex than most people know, read further to learn… . .
Keywords for this free course: . motivation, engagement, heroes, Security-Scouts, critical thinking, stay out of the box, adapt to new technologies, be aware of the malware, nobody is perfect, knowing the dangers and risks, responsibility, responsibility of School, responsibility of IT-Admin, responsibilities of BYOD users, Apple insecurity, Insecurity of Apps, Principals responsibilities, Mobile Device Management, risks of BYOD, BYOD-Policy, IT-Security Infrastructure, Teacher-Parents Meeting, Cyberwar, Cyberwarfare, Government, Internet-Safety, IT-Security knowledge basics...
The weakest link in the Security Chain is the human! If you don’t respect certain advice you will get tricked by the Cyber-Criminals!
Read more: http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/
Via Gust MEES, Lee Hall
Gary Harwell's curator insight,
April 3, 2013 12:47 AM
Is ti possible that we have a special room for this?
Imation’s portable USB desktops transform any computer into an IT-managed workstation, so workers can take all their data, applications and systems with them, securely and reliably.
Read more: http://www.imation.com/en-EU/Mobile-Security/Mobile-Security-Products/Secure-Mobile-Workspace/
Via Gust MEES |