Get Started for FREE
Sign up with Facebook Sign up with X
I don't have a Facebook or a X account
 Your new post is loading... Your new post is loading...
 Your new post is loading... Your new post is loading...

Gust MEES's curator insight,
July 4, 2013 6:45 AM
The vulnerability allows hackers to modify an app without breaking its cryptographic signature, according to Jeff Forristal, chief technology officer (CTO) at mobile security firm Bluebox. 
Gust MEES's curator insight,
July 4, 2013 6:48 AM
The vulnerability allows hackers to modify an app without breaking its cryptographic signature, according to Jeff Forristal, chief technology officer (CTO) at mobile security firm Bluebox. 
Zhao KQiang's curator insight,
March 27, 2014 6:52 AM
there is one example of smart phone security. focus on the mobile system Android

Gust MEES's curator insight,
July 2, 2013 3:01 PM
Learn more:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=Games
|

Gust MEES's curator insight,
July 18, 2013 5:33 PM
Watch log files for command instances, such as file creation and modification. However, the key point is to stay on top of updates, especially for platforms such as WordPress and Joomla, which are popular targets for attackers and constantly updated in order to address security concerns.
Learn more:
- http://gustmees.wordpress.com/2013/06/23/ict-awareness-what-you-should-know/

Gust MEES's curator insight,
July 18, 2013 5:37 PM
Watch log files for command instances, such as file creation and modification. However, the key point is to stay on top of updates, especially for platforms such as WordPress and Joomla, which are popular targets for attackers and constantly updated in order to address security concerns.
Learn more:
- http://gustmees.wordpress.com/2013/06/23/ict-awareness-what-you-should-know/
|




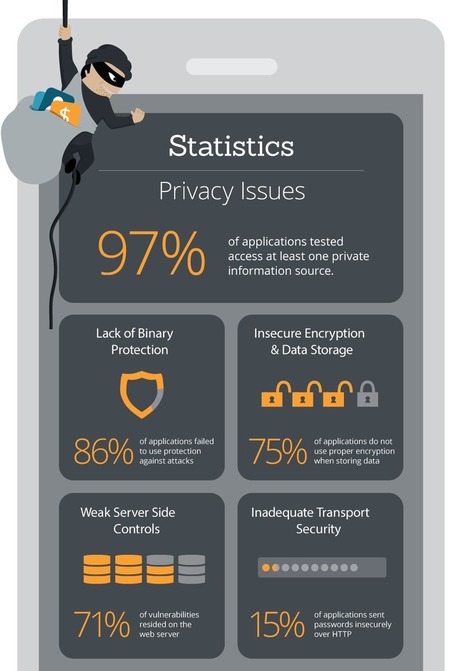







![Digital Attacks! Protect Yourself Against Cyber Threats [Infographic] | Daily Magazine | Scoop.it](https://img.scoop.it/B7yQuqAc8MxFKtFlLhEWMTl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)






Learn more:
- http://www.scoop.it/t/apps-for-any-use-mostly-for-education-and-free
Learn more:
- http://www.scoop.it/t/apps-for-any-use-mostly-for-education-and-free